 |
 |
 |
 |
Part1. Protocol Verification
Exercise 1a. Reachability Analysis
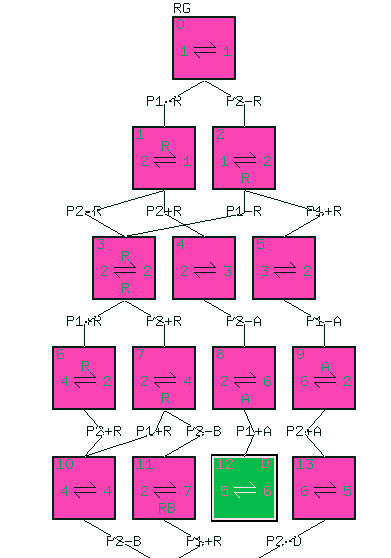
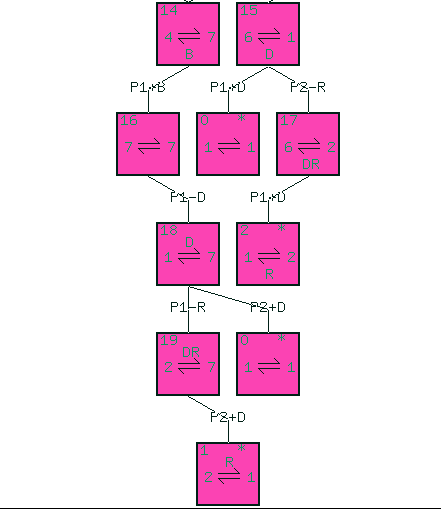
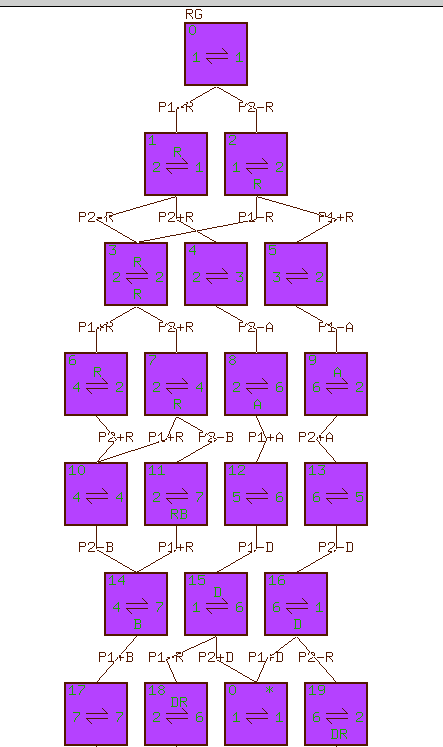
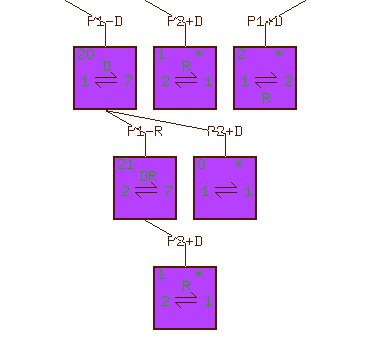
Note you can use a tool called setool to verify your reachability analysis result. The web page for using setool is at http://cs.uccs.edu/~cs522/hw/hwF2004/setool.htm
Exercise 2. Understand the protocol behavior of Alternating Bit Protocol.
1. (1, 1, E, E)—S:New Dataà(2, 1, E, E)
2. (2,
1, E, E)—S:-D0à(3,
1, D0, E)
3. (3, 1, D0, E) —R: +D0à(3,
2, E, E)
4. (3, 2, E, E)—R: Deliver Dataà(3,
3, E, E)
5. (3, 3, E, E)—R:-A0à(3,
4, E, A0)
6. (3, 4, E, A0)—A:+A0à(4, 4, E, E)
7. (4, 4, E, E)—S:New Dataà(5, 4, E, E)
8. (5, 4, E, E)—S:-D1à(6, 4, D1, E)
9. (6, 4, D1, E) —C1:Second Msg, loses D1à(6, 4, E, E)
10. (6, 4, E, E)—S:timeoutà(8, 4, E, E)
11. (8, 4, E, E)—S:-D1à(6, 4, D1, E) # this is a retransmission of D1
12. (6, 4, D1, E)—R: +D1à(6, 5, E, E) # 3rd msg on C1, C1delivers D1
13. (6, 5, E, E)—R:Deliver Dataà(6, 6, E, E)
14.
(6, 6, E, E)—R:-A1à(6,
1, E, A1)
15. (6, 1, E, A1)—C2: Second Msg, Lose A1à(6,
1, E, E)
16. (6, 1, E, E)—S:timeoutà(8,
1, E, E)
17. (8, 1, E, E)—S:-D1à(6,
1, D1, E)
18. (6, 1, D1, E)—C1:4th Msg, loses D1à(6, 1, E, E)
19. (6,
1, E, E)—S:timeoutà(8,
1, E, E)
20. (8, 1, E, E)—S:-D1à(6,
1, D1, E)
21. (6, 1, D1, E)—R:+D1à(6,
8, E, E) # 5th msg on C1, C1 delivers D1
22. (6, 8, E, E)—R:-A1à(6,
1, E, A1) # retransmission of A1
23. (6, 1, E, A1)—S:+A1à(1, 1, E, E) # This completes the first cycle of Senser's CFSM
Exercise 1c. Byte Ordering in Communications.
Part2. Protocol Implementation.
Ans: By having the sender sets the mto.src in the msg sent with its own socket info and sets mto.dst with receiver's socket info (IP address and port number), Channel C1 can then use the mto.dst in the msg received to relay the msg to the receiver. The receiver will swap the mto.src and mto.dst content and therefore the mto.dst of ACK msg sent by the receiver will contain the sender's socket info. This allows Channel C2 to use mto.dst to relay ACK msg to the sender.