SSLCertificateFile /etc/pki/tls/certs/localhost.crt
SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
- cp /etc/pki/tls/certs/localhost.crt /etc/pki/tls/certs/localhost.crt.bak
- cp /etc/pki/tls/private/localhost.key /etc/pki/tls/private/localhost.key.bak
- cp /etc/pki/tls/fc4ServerCert.pem /etc/pki/tls/certs/localhost.crt
- cp /etc/pki/tls/fc4ServerPrivateKey.pem /etc/pki/tls/private/localhost.key
127.0.0.1 fc4.csnet.uccs.edu fc4 localhost.localdomain localhost
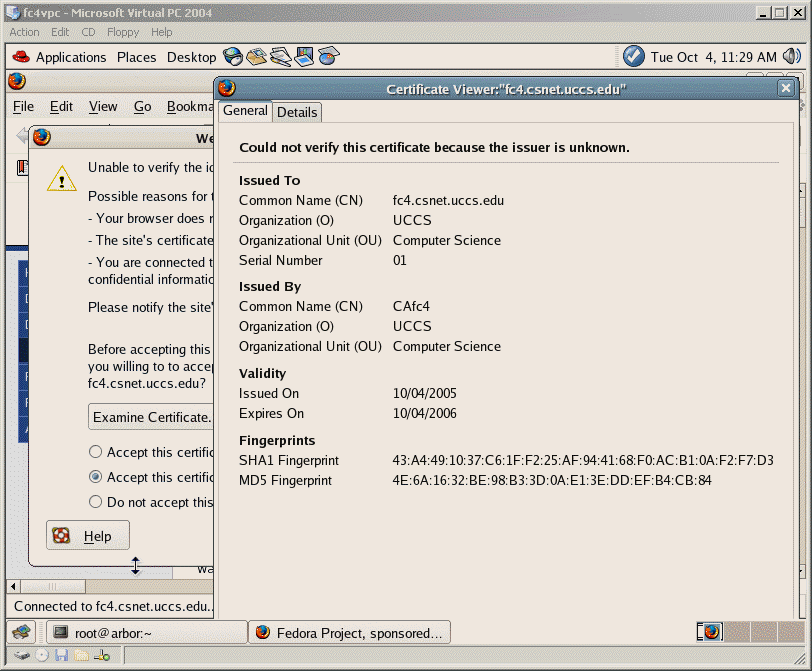
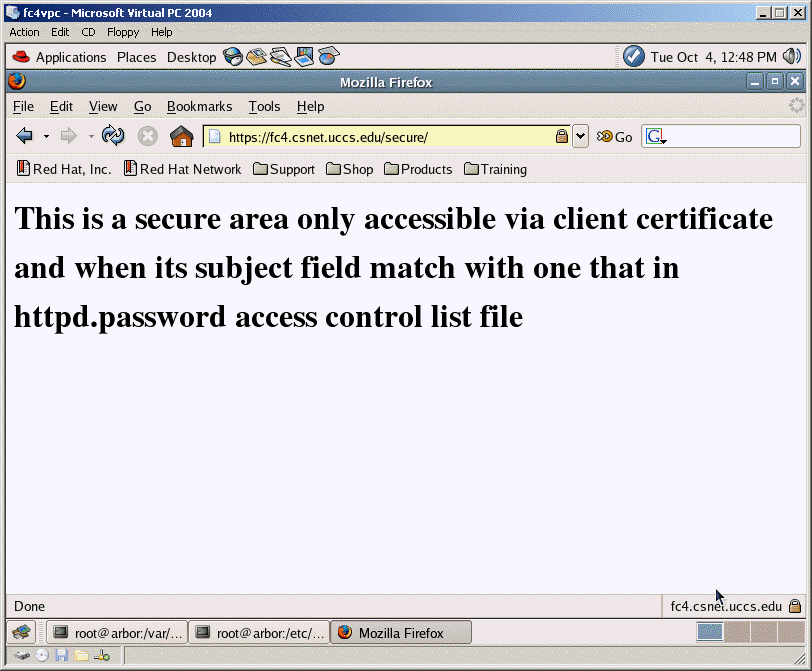
This allows us to resolve the fc4.csnet.uccs.edu domain name locally without checking with DNS system.
/etc/httpd/logs/ssl_error_log, we found the apache complains that it does not read in pass phrase.
[Sun Sep 25 15:28:05 2005] [error] Init: Unable to read pass phrase [Hint: key introduced or changed before restart?]
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,E0CD27BB7E7391A8
/B3JCpLAAL+Nx7UhWcFLtFSvZQYAAWTJKdn0PXkd4yww/m4hSzvAnIae8hs/RC3a
qVsjuuVL0KGOLwCvbTpKxC6NUCWgMjsxqzwwCOEOe839uarM1kfL1sszpqtTDMFe
CZwP8yEBBkbe72+Txllq7TVkaKPwVFTmey4T8Bk2iWc5XqYQjefTBRvBsASOlTbq
7x0nWcsLbTuAYLZbWPMweWXkODfg7uXRHOH5OLaaeiI9wFXy8PRyZFaUtKr/IoIy
e0ZVvveU3lBO+56y1KyGkys1ggqCwLvMGddVRpx7qoSL9epzjwQgaS3LndpwzIi0
HF1zaFOe3C66rkENMlh1Iz+bl2YD6bYIzYr0g3A0UZFIM70deuXH9OOioNt4+slb
Ck2zD1iqi8aIUz/CUgY3K5vTiTTuqeMCpvs5LmDOwmau3GfkwEG0Z6VAkifLmhrc
HbzLTk6q4KRCYuHhTq2snXbrxsICqvgSUJG90owgV/B3aQVpS59pi9tiuGK13xji
sH9UHF8NbTKTugApajWK7fUrVIF4duSDlilEgx+VG5KnbPErUWlJcP67emdRHk9Z
GucYpbyoNA5v1BXdcU2lmoBDQm9dyU6+eX0x6ZNopLYELM8rINr/zcFkJ4+xIz9B
eZg+EvrTyHfWRAeYVoj7yZKBLPZrnESC1Pztwx1xSZsPCkJ02H4BzzStZ0v/a3zh
KvfywfHl9hPVfUELfSaKQJaUsqAokEJeEhMlSqIhnjg7DKPqBeR7fw38fw/QUeKO
OSgfBEXAMMS+GA974rw1AvQrDlJOdpmFtB9XfkF+of2pStrcWJcuow==
-----END RSA PRIVATE KEY-----
The first two lines indicated the private key is encrypted with 3DEC encryption method and E0CD27BB7E7391A8 is the encrypted password.
If we use serverPrivateKey.pem as server.key directly, the apache web server will ask for pass phrase during the configuration time and fails if we use apachectl script.
To avoid the problem of entering the pass phrase, we can remove the pass phrase protection on the server private key with the following openssl command.
[root@fc4 tls]# cp fc4ServerPrivateKey.pem fc4ServerPrivateKey.pem.new
[root@fc4 tls]# openssl rsa -in fc4ServerPrivateKey.pem.new -out fc4ServerPrivateKey.pem
Enter pass phrase for fc4ServerPrivateKey.pem.new:
writing RSA key
[root@fc3c ssl.key]# vi fc4ServerPrivateKey.pem
-----BEGIN RSA PRIVATE KEY-----
MIICXQIBAAKBgQCjiktsmyUL31UmfktdO82doP1zCnsAgdTCfjQBCKLhip7s0l6d
XGEpBe+G4R3m0Z4nhSrofBOOls2+A9DQIykoz5fqOLdFWoqOxvwPzUWozoLlJ5LR
HMZ6UTD0SlorHWD4yCHyDg0gnb5tvtsfgGalM+cKuqx4yKVb6Qf7g8BZEQIDAQAB
AoGAF8N5sD9fA7mhEuXZJ6QP/a6uBXBpbSpwcw6JmfjaSjGtZDYxX2ZUC/T72DqP
8MFW3OFB2eRlpxuMq+a8CfKCAVupNh8rmEgIGn6qgjasledp4ifFOAwsekC7E3WY
hp1k1X8AUzZ6pS9c849zObhgWZ6vGCBvay00Se23ex7mQAECQQDO1jAA7CT8fjqA
FodWnK0K0UblKa8H1Vm4+4+x4+YV+UZUo11QCEUPkgg3QDki+zIQL9RwMrKK5rF7
eDOhpvwBAkEAymmPMi7EVRzmw8PFq2iVuCPhJt+HEWf9RAEg8RD/mBmwCUKueU/J
n+l9GDzOqlrdDgeDuXwfoop07pzL0x2dEQJAN0MW1EhDoYqAStS6GDQIL8m2bWfz
sd4Y+MmNnPPM97YASoDTX5y2BvD3bPulyGjg+V4uHkQNW/tDFEALW3doAQJBAMnv
zCvNmpQrdFJkc0XR3mTKburgYJlN/M+mrJ20TrsJDaX/f5+JqWa/g8z1hV1Rr246
swEPQ2Re68/OYE7sIXECQQCA5jLmCophfT54L3toKwWzRrwiLXdG/3x5qPQfsNv9
Q+jyRqVIQ46ecavqS803BYRUa2nId7Hx92sWAyhLBaJi
-----END RSA PRIVATE KEY-----
[root@fc4 tls]# cp /etc/pki/tls/fc4ServerPrivateKey.pem /etc/pki/tls/private/localhost.key
Save the image in your CS Unix machine web site and email me the url.