| Name | Assigned IP Addresses | Gateway | DNS names |
|---|---|---|---|
| Albright, Michael | 128.198.161.132-133 | 128.198.161.129 | malbrigh; malbrighx |
| Ashary, Ehab Bahaudien | 128.198.161.134-135 | 128.198.161.129 | eashary; easharyx |
| Bates, Andrew Leonard | 128.198.161.136-137 | 128.198.161.129 | abates; abatesx |
| Beitz, Ryan R | 128.198.161.138-139 | 128.198.161.129 | rbeitz; rbeitzx |
| Brachfeld, Lawrence Jay | 128.198.161.140-141 | 128.198.161.129 | lbrachfe; lbrachfex |
| Cabuzzi, Christopher Philip | 128.198.161.142-143 | 128.198.161.129 | ccabuzzi; ccabuzzix |
| Carey, Bryan Timothy | 128.198.161.144-145 | 128.198.161.129 | bcarey; bcareyx |
| Claes, Dennis Calvin | 128.198.161.146-147 | 128.198.161.129 | dclaes; dclaesx |
| Clonts, Michael Allen | 128.198.161.148-149 | 128.198.161.129 | mclonts; mclontsx |
| Cook, Randy Lee | 128.198.161.150-151 | 128.198.161.129 | rcook3; rcook3x |
| Helton, Richard Lee | 128.198.161.152-153 | 128.198.161.129 | rhelton; rheltonx |
| Hutchison, Troy L | 128.198.161.154-155 | 128.198.161.129 | thutchis; thutchisx |
| Iyer, Vijay Navin | 128.198.161.156-157 | 128.198.161.129 | viyer; viyerx |
| Jost, Richard Clarkson | 128.198.161.164-165 | 128.198.161.161 | rjost; rjostx |
| Karikatti, Smita | 128.198.161.166-167 | 128.198.161.161 | skarikat; skarikatx |
| Kimzey, Robin Tracy | 128.198.161.168-169 | 128.198.161.161 | rkimzey; rkimzeyx |
| Lykins, Rodney D | 128.198.161.170-171 | 128.198.161.161 | rlykins; rlykinsx |
| Magut, Sheila Jeruto | 128.198.161.172-173 | 128.198.161.161 | smagut; smagutx |
| Mudrak, George Francis | 128.198.161.174-175 | 128.198.161.161 | gmudrak; gmudrakx |
| Navamani, Beaulah Aloysius | 128.198.161.176-177 | 128.198.161.161 | bnavaman; bnavamanx |
| Padubrin, Harry Friedbert | 128.198.161.178-179 | 128.198.161.161 | hpadubri; hpadubrix |
| Parris, Jonathan David | 128.198.161.180-181 | 128.198.161.161 | jparris; jparrisx |
| Rajagopal, Suresh | 128.198.161.182-183 | 128.198.161.161 | srajagop; srajagopx |
| Sheneamer, Abdullah Mohammad | 128.198.161.184-185 | 128.198.161.161 | asheneam; asheneamx |
| Sostheim, Angelica Louise | 128.198.161.186-187 | 128.198.161.161 | asosthei; asostheix |
| Thorpe, Donovan | 128.198.161.188-189 | 128.198.161.161 | dthorpe; dthorpex |
| Turnerjr, George Eugene | 128.198.161.216-217 | 128.198.161.193 | gturner4; gturner4x |
| Walters, Russell Tyson | 128.198.161.218-219 | 128.198.161.193 | rwalter3; rwalter3x |
| Williams, Gregory L | 128.198.161.220-221 | 128.198.161.193 | gwillia5; gwillia5x |
| cs591 | 128.198.161.212-213 | 128.198.161.193 | cs591; cs591x |
| Chow, Edward | 128.198.161.214-215 | 128.198.161.193 | chow; chowx |
Server: 128.198.60.194
Address: 128.198.60.194#53
Name: bcareyx.csnet.uccs.edu
Address: 128.198.161.145
- . Those with 128.198.161.129" gateway should choose dvPortGroup VLAN 366 (by default). 128.198.161.128/27 subent.
- Those with 128.198.161.161 gateway, should choose dvPortGroup VLAN 367. 128.198.161.160/27 subnet.
- Those with 128.198.161.193 gateway should choose dvPortGroup VLAN 368. 128.198.161.192/27 subnet.
- Select the right VM network (VMNet 366, VMNet 367, or VMNet 368). On the "Gettign Started" tab, select "Edit virtual machine settings". Then select the "Network Adapter 1", On the "Network label" dropdown menu" select the proper "VM Network" associated with your subnet. Those with 128.198.161.129" gateway should choose VMNet 366 (by default). Those with 128.198.161.161 gateway, should choose VMNet 367. Those with 128.198.161.193 gateway should choose VMnet 368.
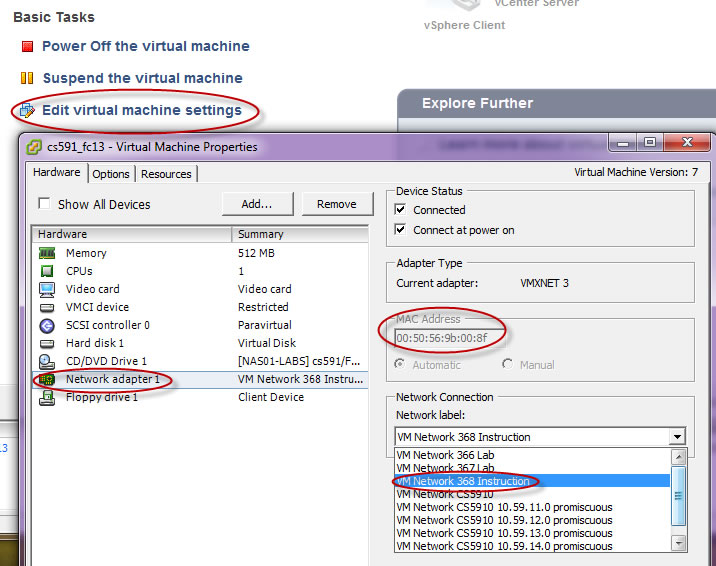
- Note that the MAC address of the clone machine network interface is changed to 00:50;56:9b:00:8f
- Rename the network interface from eth1 to eth0
- During the cloning process, the vsphere change the mac address of the cloned virtual machine so that it will not collide with that of the original or other cloned virtual machines. How to make that uniques? All 30 clone vm needs to have unique mac address.
- Edit udev configuration file, "vi /etc/udev/rules.d/70-persistent-net.rules"
- It has the followign content
# This file was automatically generated by the /lib/udev/write_net_rules # program, run by the persistent-net-generator.rules rules file. # # You can modify it, as long as you keep each rule on a single # line, and change only the value of the NAME= key. # PCI device 0x15ad:0x07b0 (vmxnet3) (custom name provided by external tool) SUBSYSTEM=="net", ACTION=="add", DRIVERS=="?*", ATTR{address}=="00:50:56:9b:00:02", ATTR{dev_id}=="0x0", ATTR{type}=="1", KERNEL=="eth*", NAME="eth0" # PCI device 0x15ad:0x07b0 (vmxnet3) SUBSYSTEM=="net", ACTION=="add", DRIVERS=="?*", ATTR{address}=="00:50:56:9b:00:8f", ATTR{dev_id}=="0x0", ATTR{type}=="1", KERNEL=="eth*", NAME="eth1" - Change the eth0 to eth1 and eth1 to eth0.
- Configure IP address with ifconfig
- Edit /etc/sysconfig/network-scripts/ifcfg-eth0 by changing the mac (HWADDR) address, gateway and ip address (your first IP address). This is the file read by the OS during the boot time to configure the network interface.
# VMware VMXNET3 Ethernet Controller DEVICE=eth0 HWADDR=00:50:56:9B:00:02 ONBOOT=yes DNS1=128.198.60.194 GATEWAY=128.198.161.129 IPADDR=128.198.161.132 NETMASK=255.255.255.224 TYPE=Ethernet BOOTPROTO=none PREFIX=27 DEFROUTE=yes IPV4_FAILURE_FATAL=yes IPV6INIT=no NAME="System eth0" UUID=5fb06bd0-0bb0-7ffb-45f1-d6edd65f3e03
- For cs591 account, I will replace GATEWAY with 128.198.161.193 and IPADDR with 128.198.161.212, HWADDR with 00:50:56:9B:00:8F
- Edit /etc/sysconfig/network-scripts/ifcfg-eth0 by changing the mac (HWADDR) address, gateway and ip address (your first IP address). This is the file read by the OS during the boot time to configure the network interface.
- Configure the resolv.conf for DNS search sequence and name server.
- Edit /etc/resolv.conf file
- Add "search csnet.uccs.edu" for the default domain name suffix.
- Add "nameserver 128.198.60.194" or other name server ip address, in order of primary, secondary, tenary name server. I believe the primary server entry already there. Just to make sure.
- Configure the hostname
- Edit /etc/sysconfig/network file
- replace HOSTNAME=fc13.csnet.uccs.edu with HOSTNAME=<yourlogin>.csnet.uccs.edu
- Reboot the machine with "reboot"
- After login, verify your new settings with "ifconfig -a" and "netstat -rn". use "ping 128.198.1.250" to make sure you can connect to the Internet. you should see the root login prompt changes from root@fc13 to root @cs591 if cs591 is your login name.
- Once your network connection is up, you can use the SSH secure shell or putty to connect to your virtual machine and make it easier to copy and past commands or session results.
- Edit /etc/pki/tls/openssl.cnf
- Change line 130: countryName_default = XX --> countryName_default = US
- Change line 135: #stateOrProvinceName_default = Default Province --> stateOrProvinceName_default = CO
- Change line 138: localityName_default = Default City --> localityName_default = Colorado Springs
- Chagne line 141: 0.organizationName_default = Default Company Ltd
--> 0.organizationName_default = UCCS - Change line 148: #organizationalUnitName_default =
--> organizationalUnitName_default = CS - Since there may be an existing CA created before, we need to remove the existing /etc/pki/CA directory so that the misc/CA -newca can perform correctly.
[root@cs591 tls]# rm /etc/pki/CA
- Proceed use "misc/CA - newca" command to create CA directory in /etc/pki/tls and create private key and certificate request, and self signed CA certficate.
[root@cs591 tls]# misc/CA -newca CA certificate filename (or enter to create) Making CA certificate ... Generating a 2048 bit RSA private key ...........................+++ ........................................................+++ writing new private key to '/etc/pki/CA/private/./cakey.pem' Enter PEM pass phrase: <enter pass phrase> Verifying - Enter PEM pass phrase: <confirm pass phrase> ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [US]: State or Province Name (full name) [CO]: Locality Name (eg, city) [Colorado Sprigns]: Organization Name (eg, company) [UCCS]: Organizational Unit Name (eg, section) [CS]: Common Name (eg, your name or your server's hostname) []:cs591CA <your loginname followed by CA> Email Address []:cs591@uccs.edu Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Using configuration from /etc/pki/tls/openssl.cnf Enter pass phrase for /etc/pki/CA/private/./cakey.pem: <entee the pass phrase> Check that the request matches the signature Signature ok Certificate Details: Serial Number: f8:f2:5d:7c:87:e1:1a:46 Validity Not Before: Oct 4 22:44:56 2010 GMT Not After : Oct 3 22:44:56 2013 GMT Subject: countryName = US stateOrProvinceName = CO organizationName = UCCS organizationalUnitName = CS commonName = cs591CA emailAddress = cs591@uccs.edu X509v3 extensions: X509v3 Subject Key Identifier: AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 X509v3 Authority Key Identifier: keyid:AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 X509v3 Basic Constraints: CA:TRUE Certificate is to be certified until Oct 3 22:44:56 2013 GMT (1095 days) Write out database with 1 new entries Data Base Updated
-
[root@cs591 tls]# misc/CA -newreq Generating a 2048 bit RSA private key .....+++ .+++ writing new private key to 'newkey.pem' Enter PEM pass phrase: Verifying - Enter PEM pass phrase: <server pass phrase> ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [US]: State or Province Name (full name) [CO]: Locality Name (eg, city) [Colorado Sprigns]: Organization Name (eg, company) [UCCS]: Organizational Unit Name (eg, section) [CS]: Common Name (eg, your name or your server's hostname) []:cs591.csnet.ucs.edu Use server full qualified DNS name (Important!) Email Address []:webmaster@cs591.csnet.uccs.edu Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Request is in newreq.pem, private key is in newkey.pem [root@cs591 tls]# cp newreq.pem cs591ServerReq.pem [root@cs591 tls]# cp newkey.pem cs591Serverkey.pem [root@cs591 tls]# misc/CA -sign Using configuration from /etc/pki/tls/openssl.cnf Enter pass phrase for /etc/pki/CA/private/cakey.pem: Check that the request matches the signature Signature ok Certificate Details: Serial Number: f8:f2:5d:7c:87:e1:1a:47 Validity Not Before: Oct 4 22:53:55 2010 GMT Not After : Oct 1 22:53:55 2020 GMT Subject: countryName = US stateOrProvinceName = CO localityName = Colorado Sprigns organizationName = UCCS organizationalUnitName = CS commonName = cs591.csnet.uccs.edu emailAddress = webmaster@cs591.csnetuccs.edu X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: FA:34:98:0B:F4:F5:D4:FD:E1:85:B1:81:A5:94:AE:3E:BD:E4:64:EA X509v3 Authority Key Identifier: keyid:AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 Certificate is to be certified until Oct 1 22:53:55 2020 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated Certificate: Data: Version: 3 (0x2) Serial Number: f8:f2:5d:7c:87:e1:1a:47 Signature Algorithm: sha1WithRSAEncryption Issuer: C=US, ST=CO, O=UCCS, OU=CS, CN=cs591CA/emailAddress=cs591@uccs.edu Validity Not Before: Oct 4 22:53:55 2010 GMT Not After : Oct 1 22:53:55 2020 GMT Subject: C=US, ST=CO, L=Colorado Sprigns, O=UCCS, OU=CS, CN=cs591.csnet.uccs.edu/emailAddress=webmaser@cs591.csnet.uccs.edu Subject Public Key Info: Public Key Algorithm: rsaEncryption Public-Key: (2048 bit) Modulus: 00:de:71:2e:d6:8e:0f:39:e1:82:a9:7d:a0:25:ba: 77:40:a2:23:74:e8:b8:ae:ac:c8:69:f5:4d:ca:3f: e9:16:73:aa:84:eb:3b:ad:7e:52:f0:6a:4b:dc:bb: 33:7b:4f:3a:f4:fd:a9:97:27:48:53:cf:5d:7d:5e: 77:01:c0:df:01:8d:98:16:c6:8d:28:b8:ca:f6:6f: 4d:0a:68:e1:cf:7a:d0:65:8c:30:6f:32:41:33:02: 04:0f:44:e8:c5:cf:ca:f2:4b:0f:09:8a:46:9e:25: 19:9b:1e:46:5d:1a:70:ba:b0:44:55:58:de:c9:c2: 26:df:c6:65:a5:96:63:5a:cc:73:5d:50:5f:b2:1c: d1:84:4e:dc:81:9c:11:30:a1:ab:52:14:dd:c5:65: 64:0d:ba:5d:5f:96:03:70:a4:0f:23:c6:3a:67:d8: 8b:d8:d1:37:08:5c:f6:65:4c:9f:b5:e5:22:c4:cc: 87:51:33:2a:73:b3:82:80:62:e9:cf:cd:5d:2a:c7: 93:fc:1b:93:58:b2:0e:b9:fb:75:bb:ca:e6:99:69: dc:06:ec:68:8b:da:cd:71:4b:79:20:50:56:d0:46: 76:e1:81:30:ec:d4:28:3a:4a:b2:55:a0:e7:34:b4: 62:ba:a1:28:2f:ee:6b:48:3c:b3:9e:d2:c4:0e:2c: 02:f1 Exponent: 65537 (0x10001) X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: FA:34:98:0B:F4:F5:D4:FD:E1:85:B1:81:A5:94:AE:3E:BD:E4:64:EA X509v3 Authority Key Identifier: keyid:AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 Signature Algorithm: sha1WithRSAEncryption 90:b0:6d:66:52:ae:f3:6c:43:ee:38:ad:b1:f7:15:0c:fe:f0: 7f:0e:a2:7e:f9:68:e0:c5:6d:38:82:7d:a0:10:bf:b2:7b:4b: a0:eb:61:ed:4d:c1:ad:be:ae:85:9e:a1:b1:87:69:e8:a8:e4: 5c:3d:19:43:f2:3a:65:cd:ac:c5:86:8d:20:7c:b3:6d:59:6f: 97:4f:74:1e:60:fe:98:22:ad:c6:54:74:ba:df:31:2e:8f:3e: 6b:5a:78:57:f0:32:ed:d2:9b:bc:0c:d5:83:fe:5e:16:85:74: d7:a5:f3:d4:92:5a:08:c9:d9:0f:eb:20:4e:66:60:34:6f:27: 64:4d:fe:39:12:5c:b3:d9:4d:e9:fb:55:63:a8:d0:63:a3:e7: e3:c2:3d:28:67:fa:8a:39:2b:6f:f1:16:09:37:c1:48:03:de: 32:43:5c:8c:78:40:8f:9e:39:8e:5a:ff:86:2c:dc:d8:f6:b5: b4:da:e1:7c:34:e9:1f:01:da:a5:82:16:7e:84:bc:57:f9:55: 90:65:0b:ca:dd:f9:3c:ec:aa:6a:a5:d5:46:5f:d5:dc:58:b5: b2:0d:b8:a1:fc:e0:ae:2f:8d:38:3f:e4:c1:70:58:7c:0c:90: ac:01:6a:5a:4a:56:a4:73:13:d5:0e:22:86:67:5d:b0:70:5e: df:5c:17:9a -----BEGIN CERTIFICATE----- MIID5jCCAs6gAwIBAgIJAPjyXXyH4RpHMA0GCSqGSIb3DQEBBQUAMGcxCzAJBgNV BAYTAlVTMQswCQYDVQQIDAJDTzENMAsGA1UECgwEVUNDUzELMAkGA1UECwwCQ1Mx EDAOBgNVBAMMB2NzNTkxQ0ExHTAbBgkqhkiG9w0BCQEWDmNzNTkxQHVjY3MuZWR1 MB4XDTEwMTAwNDIyNTM1NVoXDTIwMTAwMTIyNTM1NVowgYAxCzAJBgNVBAYTAlVT MQswCQYDVQQIDAJDTzEZMBcGA1UEBwwQQ29sb3JhZG8gU3ByaWduczENMAsGA1UE CgwEVUNDUzELMAkGA1UECwwCQ1MxDjAMBgNVBAMMBWNzNTkxMR0wGwYJKoZIhvcN AQkBFg5jczU5MUB1Y2NzLmVkdTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoC ggEBAN5xLtaODznhgql9oCW6d0CiI3TouK6syGn1Tco/6RZzqoTrO61+UvBqS9y7 M3tPOvT9qZcnSFPPXX1edwHA3wGNmBbGjSi4yvZvTQpo4c960GWMMG8yQTMCBA9E 6MXPyvJLDwmKRp4lGZseRl0acLqwRFVY3snCJt/GZaWWY1rMc11QX7Ic0YRO3IGc ETChq1IU3cVlZA26XV+WA3CkDyPGOmfYi9jRNwhc9mVMn7XlIsTMh1EzKnOzgoBi 6c/NXSrHk/wbk1iyDrn7dbvK5plp3AbsaIvazXFLeSBQVtBGduGBMOzUKDpKslWg 5zS0YrqhKC/ua0g8s57SxA4sAvECAwEAAaN7MHkwCQYDVR0TBAIwADAsBglghkgB hvhCAQ0EHxYdT3BlblNTTCBHZW5lcmF0ZWQgQ2VydGlmaWNhdGUwHQYDVR0OBBYE FPo0mAv09dT94YWxgaWUrj695GTqMB8GA1UdIwQYMBaAFK2LWb0fkdXNMYIPih3M 5EGkQUxXMA0GCSqGSIb3DQEBBQUAA4IBAQCQsG1mUq7zbEPuOK2x9xUM/vB/DqJ+ +WjgxW04gn2gEL+ye0ug62HtTcGtvq6FnqGxh2noqORcPRlD8jplzazFho0gfLNt WW+XT3QeYP6YIq3GVHS63zEujz5rWnhX8DLt0pu8DNWD/l4WhXTXpfPUkloIydkP 6yBOZmA0bydkTf45Elyz2U3p+1VjqNBjo+fjwj0oZ/qKOStv8RYJN8FIA94yQ1yM eECPnjmOWv+GLNzY9rW02uF8NOkfAdqlghZ+hLxX+VWQZQvK3fk87KpqpdVGX9Xc WLWyDbih/OCuL404P+TBcFh8DJCsAWpaSlakcxPVDiKGZ12wcF7fXBea -----END CERTIFICATE----- Signed certificate is in newcert.pem [root@cs591 tls]# cp newcert.pem cs591ServerCert.pem
- apache secure web access configuration file is located in /etc/httpd/conf.d/ssl.conf
- Lines 101-113 indicates the locations for server certificate and private key
# Server Certificate: # Point SSLCertificateFile at a PEM encoded certificate. If # the certificate is encrypted, then you will be prompted for a # pass phrase. Note that a kill -HUP will prompt again. A new # certificate can be generated using the genkey(1) command. SSLCertificateFile /etc/pki/tls/certs/localhost.crt # Server Private Key: # If the key is not combined with the certificate, use this # directive to point at the key file. Keep in mind that if # you've both a RSA and a DSA private key you can configure # both in parallel (to also allow the use of DSA ciphers, etc.) SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
- Let us copy the server key and certificate there.
- cp cs591ServerKey.pem /etc/pki/tls/private/localhost.key
- cp cs591ServerCert.pem /etc/pki/tls/certs/localhost.crt
- remove the pass phrase protection on private key so that when the httpd reboot it does not have to wait for the system admin to enter the root password (which could be at 3am!). We will reply on file access control to protect the privatekey.
- cd /etc/pki/tls/private
- openssl rsa -in localhost.key -out server.key
- mv localhost.key localhost.key.enc
- mv server.key localhost.key
- service httpd restart
- verify secure web site access. Then type "https://cs591.csnet.uccs.edu" where cs591 is replaced with your login.
- Take a snapshot of the server certificate presented by your apache web server. Save the snapshot in your CS591 personal web page directory. Submit the url of the snapshot as part of your hw2 p5 deliverable.
- If web server is blocked by firewall on your server, try "lokkit -p https:tcp" to allow access.
- Edit /etc/httpd/conf.d/ssl.conf file to include the following content right after line 135 to protect the /var/www/html/secure directory with "http://<login>.csnet.uccs.edu/secure" as url.
- The above was not correct. we need to put the following in the /etc/httpd/conf/httpd.conf (at the end of the file is fine) to protect secure directory being access from plain httpd access.
SSLVerifyClient none <Directory /var/www/html/secure> SSLVerifyClient require SSLVerifyDepth 5 SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt SSLOptions +FakeBasicAuth SSLRequireSSL AuthName "UCCS CS Department" AuthType Basic AuthUserFile /etc/httpd/conf/httpd.passwd require valid-user </Directory> - Set up password file to further restrict access based on subject field of client certificate.
- Create httpd.passwd file in /etc/httpd/conf/. Add the following line (single line no break) to it
/C=US/ST=CO/L=Colorado Springs/O=UCCS/OU=CS/CN=cs591/emailAddress=cs591@uccs.edu:xxj31ZMTZzkVA - Replace cs591 with your login name in the above password line.
- Only those users, who present a client certificate with subject field containing the exact content, will be allowed to access /var/www/html/secure directory.
- The above client certificate verification using FakeBasicAuth option is implemented in line1836 of ssl_hook_UserCheck() of ssl_engine_kernel.c.
http://cs.uccs.edu/~cs591/httpd-2.0.54/modules/ssl/ssl_engine_kernel.c - Note that string "xxj31ZMTZzkVA" is used as the password in the user file and it is just the crypted variant of the word "password".
- Create httpd.passwd file in /etc/httpd/conf/. Add the following line (single line no break) to it
- Set up a secure web page fyi.html in /var/www/html/secure with the following content.
<h1>For your eyes only, created by <your name> on <your IP address> </h1> - Set up apache to access list of CAs in ca-bundle.crt for verifying certificates signed by these CAs.
- Edit /etc/httpd/conf.d/ssl.conf uncomment line 128
SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
- Add our CA to the ca-bundle.crt
cp /etc/pki/tls/certs/ca-bundle.crt /etc/pki/tls/certs/ca-bundle.crt.bak
cat /etc/pki/tls/certs/ca-bundle.crt /etc/pki/CA/cacert.pem > newca-bundle.crt
cp newca-bundle.crt ca-bundle.crt
- Edit /etc/httpd/conf.d/ssl.conf uncomment line 128
- create/sign personal certificate.
[root@cs591 tls]# misc/CA -newreq Generating a 2048 bit RSA private key .................+++ .+++ writing new private key to 'newkey.pem' Enter PEM pass phrase: Verifying - Enter PEM pass phrase: ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [US]: State or Province Name (full name) [CO]: Locality Name (eg, city) [Colorado Sprigns]: Organization Name (eg, company) [UCCS]: Organizational Unit Name (eg, section) [CS]: Common Name (eg, your name or your server's hostname) []:cchow Email Address []:cchow@uccs.edu Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Request is in newreq.pem, private key is in newkey.pem [root@cs591 tls]# cp newkey.pem cchowKey.pem [root@cs591 tls]# misc/CA -sign Using configuration from /etc/pki/tls/openssl.cnf Enter pass phrase for /etc/pki/CA/private/cakey.pem: Check that the request matches the signature Signature ok Certificate Details: Serial Number: f8:f2:5d:7c:87:e1:1a:48 Validity Not Before: Oct 5 19:49:13 2010 GMT Not After : Oct 2 19:49:13 2020 GMT Subject: countryName = US stateOrProvinceName = CO localityName = Colorado Sprigns organizationName = UCCS organizationalUnitName = CS commonName = cchow emailAddress = cchow@uccs.edu X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 41:7E:84:7D:77:35:C6:24:C8:BD:E6:7C:89:31:6F:69:82:86:C4:97 X509v3 Authority Key Identifier: keyid:AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 Certificate is to be certified until Oct 2 19:49:13 2020 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated Certificate: Data: Version: 3 (0x2) Serial Number: f8:f2:5d:7c:87:e1:1a:48 Signature Algorithm: sha1WithRSAEncryption Issuer: C=US, ST=CO, O=UCCS, OU=CS, CN=cs591CA/emailAddress=cs591@uccs.edu Validity Not Before: Oct 5 19:49:13 2010 GMT Not After : Oct 2 19:49:13 2020 GMT Subject: C=US, ST=CO, L=Colorado Sprigns, O=UCCS, OU=CS, CN=cchow/emailAddress=cchow@uccs.edu Subject Public Key Info: Public Key Algorithm: rsaEncryption Public-Key: (2048 bit) Modulus: 00:c7:c6:e0:f7:03:1d:83:9d:fa:4d:b1:cc:59:66: a5:ff:5e:2b:01:36:d9:79:30:3d:e3:22:71:c7:cc: ff:3b:f5:08:e2:96:f6:48:ff:e1:69:88:88:87:47: 69:af:b5:69:b8:9a:20:95:50:a7:05:52:15:af:c6: 42:95:91:86:0e:75:2f:d6:56:aa:2c:7f:22:8f:0b: d1:2f:0c:d3:fc:d6:a0:90:06:5f:10:8f:38:d8:de: 05:3d:93:f8:62:c2:5f:1d:9e:ac:a8:2b:51:75:64: 57:49:d9:e7:87:df:aa:77:20:b2:ef:cf:f6:3a:e2: e3:d4:a5:cc:ac:e0:6d:01:28:ed:bd:78:94:ca:8f: 26:0e:b8:73:fd:ab:d3:e5:bb:d7:6a:be:f9:e6:65: 84:39:3a:54:48:5f:da:a8:03:45:a4:29:33:ec:e1: 87:35:ed:6a:f3:ad:2c:32:43:99:fd:80:a3:bd:76: f5:b9:d0:29:b7:21:5e:78:c3:d9:d8:a4:e3:aa:4e: d1:a5:4b:8f:d7:75:67:2e:4d:1c:0b:7e:eb:ae:55: 11:ed:4a:11:e0:63:f4:c3:27:2f:33:34:b7:4a:16: 5a:5b:3b:64:7e:05:06:2b:d2:37:6c:4a:f9:ba:30: 39:09:d8:7e:0d:80:b0:2b:41:9a:05:12:85:64:2e: ca:2b Exponent: 65537 (0x10001) X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 41:7E:84:7D:77:35:C6:24:C8:BD:E6:7C:89:31:6F:69:82:86:C4:97 X509v3 Authority Key Identifier: keyid:AD:8B:59:BD:1F:91:D5:CD:31:82:0F:8A:1D:CC:E4:41:A4:41:4C:57 Signature Algorithm: sha1WithRSAEncryption 4e:65:9d:c0:67:1a:68:ce:94:58:93:27:c3:bb:36:e4:92:b7: 08:9d:ff:4f:37:03:c7:12:25:75:da:6a:53:e7:d7:1c:58:d0: 62:2f:41:32:34:16:de:a8:39:d4:81:76:f4:d3:17:70:ba:bc: 2a:f4:d6:c2:57:df:a5:2d:a5:60:56:29:95:c4:97:78:c4:39: 7f:de:10:a9:59:4c:52:d0:40:ae:f8:84:fd:c2:a4:71:12:ab: d1:c7:36:e3:60:0c:25:4b:ce:f0:a5:07:2b:ec:08:d7:6c:d0: a4:80:91:ff:5d:62:63:20:9f:bf:cf:d8:23:3e:32:cd:c9:42: 17:7f:0a:49:57:2b:a1:39:0d:a7:79:7d:70:19:a5:1f:9f:4f: 3d:1a:e1:05:72:49:8d:bb:1e:a3:d9:e7:2b:09:08:b2:bb:66: b8:37:51:33:8e:08:10:34:31:24:e5:3f:c0:e0:ea:9f:00:ae: a9:51:05:05:db:ba:ef:3e:b3:72:1b:b9:40:6d:3b:7e:d7:84: 5a:0f:f5:8a:2b:a9:be:23:a7:7c:02:5f:b9:02:75:b6:7b:37: 2b:39:54:ba:5e:54:58:73:04:fe:ce:33:3a:3c:87:bb:13:85: 27:4a:6c:c0:6c:24:1c:33:35:75:e2:dd:e7:ba:cf:00:3e:60: bb:cf:97:73 -----BEGIN CERTIFICATE----- MIID5jCCAs6gAwIBAgIJAPjyXXyH4RpIMA0GCSqGSIb3DQEBBQUAMGcxCzAJBgNV BAYTAlVTMQswCQYDVQQIDAJDTzENMAsGA1UECgwEVUNDUzELMAkGA1UECwwCQ1Mx EDAOBgNVBAMMB2NzNTkxQ0ExHTAbBgkqhkiG9w0BCQEWDmNzNTkxQHVjY3MuZWR1 MB4XDTEwMTAwNTE5NDkxM1oXDTIwMTAwMjE5NDkxM1owgYAxCzAJBgNVBAYTAlVT MQswCQYDVQQIDAJDTzEZMBcGA1UEBwwQQ29sb3JhZG8gU3ByaWduczENMAsGA1UE CgwEVUNDUzELMAkGA1UECwwCQ1MxDjAMBgNVBAMMBWNjaG93MR0wGwYJKoZIhvcN AQkBFg5jY2hvd0B1Y2NzLmVkdTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoC ggEBAMfG4PcDHYOd+k2xzFlmpf9eKwE22XkwPeMiccfM/zv1COKW9kj/4WmIiIdH aa+1abiaIJVQpwVSFa/GQpWRhg51L9ZWqix/Io8L0S8M0/zWoJAGXxCPONjeBT2T +GLCXx2erKgrUXVkV0nZ54ffqncgsu/P9jri49SlzKzgbQEo7b14lMqPJg64c/2r 0+W712q++eZlhDk6VEhf2qgDRaQpM+zhhzXtavOtLDJDmf2Ao7129bnQKbchXnjD 2dik46pO0aVLj9d1Zy5NHAt+665VEe1KEeBj9MMnLzM0t0oWWls7ZH4FBivSN2xK +bowOQnYfg2AsCtBmgUShWQuyisCAwEAAaN7MHkwCQYDVR0TBAIwADAsBglghkgB hvhCAQ0EHxYdT3BlblNTTCBHZW5lcmF0ZWQgQ2VydGlmaWNhdGUwHQYDVR0OBBYE FEF+hH13NcYkyL3mfIkxb2mChsSXMB8GA1UdIwQYMBaAFK2LWb0fkdXNMYIPih3M 5EGkQUxXMA0GCSqGSIb3DQEBBQUAA4IBAQBOZZ3AZxpozpRYkyfDuzbkkrcInf9P NwPHEiV12mpT59ccWNBiL0EyNBbeqDnUgXb00xdwurwq9NbCV9+lLaVgVimVxJd4 xDl/3hCpWUxS0ECu+IT9wqRxEqvRxzbjYAwlS87wpQcr7AjXbNCkgJH/XWJjIJ+/ z9gjPjLNyUIXfwpJVyuhOQ2neX1wGaUfn089GuEFckmNux6j2ecrCQiyu2a4N1Ez jggQNDEk5T/A4OqfAK6pUQUF27rvPrNyG7lAbTt+14RaD/WKK6m+I6d8Al+5AnW2 ezcrOVS6XlRYcwT+zjM6PIe7E4UnSmzAbCQcMzV14t3nus8APmC7z5dz -----END CERTIFICATE----- Signed certificate is in newcert.pem [root@cs591 tls]# cp newcert.pem cchowCert.pem [root@cs591 tls]# openssl pkcs12 -export -in cchowCert.pem -inkey cchowKey.pem -out cchowClient.p12 Enter pass phrase for cchowKey.pem: Enter Export Password: Verifying - Enter Export Password: [root@cs591 tls]# ls cchowCert.pem certs misc openssl.cnf cchowClient.p12 cs591ServerCert.pem newcert.pem private cchowKey.pem cs591ServerKey.pem newkey.pem cert.pem cs591ServerReq.pem newreq.pem
- Create/sign csnet client certificate. Repeat the above procedure and use csnet as common name and csnet@uccs.edu as email, Save the combined key and certificate as csnetClient.p12 file.
- make a plain web directory for saving the certificate related files.
mkdir /var/www/html/plain - copy the two .p12 files to your server web site for future download to your browser.
cp *.p12 /var/www/html/plain - copy the cacert.pem file in /etc/pki/CA to /var/www/html/plain
- On your brower, retrieve the cacert.pem and client .p12 files with http://128.198.161.212/plain directory Replace 128.198.161.212 with the IP address you used to configure your vm.
- Set up browser for mutual autentication
- Import .p12 file into your browser. By clicking on the .p12 file. on my desktop, it triggers the certificate import wizard. I need to type in the export password which protect the .p12 file.
- Import .p12 file into your browser. By clicking on the .p12 file. on my desktop, it triggers the certificate import wizard. I need to type in the export password which protect the .p12 file.
- Set up browser for mutual autentication
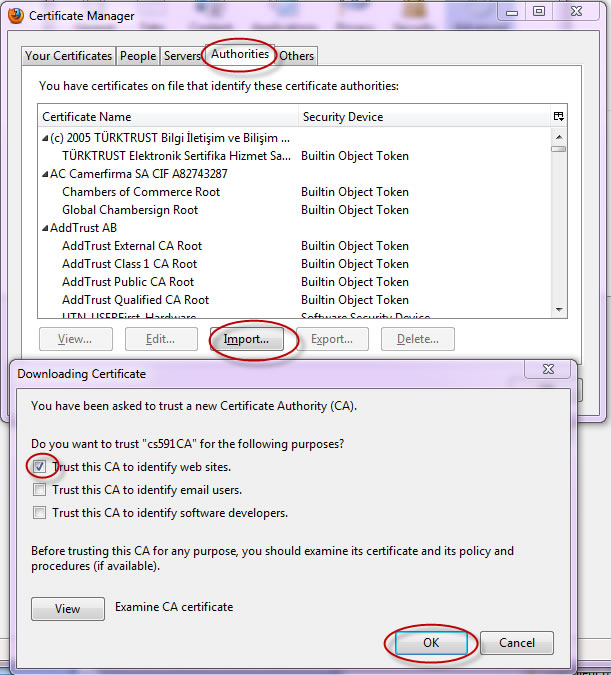
- Install cacert.pem on browser to trust your CA.
- on Firefox, select "tools" menu, and "option" menuitem. Then click the "Advanced" icon, the "view certificates" button.
- Make sure "Ask me very time" choice button is selected, so that the browser will ask you to choose the proper client certificate.
- click on Authorirties tab on Certificate manager, then click "import" button. Select the cacert.pem file.
- On IE, you select "Tools" menu, "Internet options" menuitem, then "content" tab, "certificate" button" to access certificate manager.
- type https://cs591.csnet.ucs.edu/secure/fyi.html to access the secure web page. Replace cs591 in url with your loginname. You will be prompt to select on one of the two client certificate. Select the one which specifies in the httpd.passwd file will grant the access. The other will be rejected. If you see the login/pasword prompt that means you are rejected. Check /etc/httpd/logs/ssl_access_log and ssl_error_log to see for the reasons.
- save the ssl_access_log in your personal cs591 directory and include the url of the ssl_access_log as your deliverablez. It should indicate the success of access using your client certificate and the denial of access using csnet client certificate
- .
- I configure openssl.cnf wrong and result in errors. By comaring the access log entry with httpd.password file, I foudn I got an typo Sprign instead of Springs. I changed the httpd.passwd file to allow access.
128.198.168.40 - /C=US/ST=CO/L=Colorado Sprigns/O=UCCS/OU=CS/CN=cchow/emailAddress=cchow@uccs.edu [05/Oct/2010:16:12:24 -0600] "GET /secure/fyi.html HTTP/1.1" 401 488 - For this mutual authentication exercise, you should not need to enter login/password. Just by choosing the proper client certificate, you should be able to access the secure web pages.