Homework #4: Configure a Secure Site with DMZ Zone with Linux Firewalls.
Goal:
- Understand firewalls, related seurity policies and security design principles.
- Learn how to use iptables provided in the Linux netfilter to construct a
site with DMZ hosting servers exposed to Internet.
- Review the basic route commands for setting up the Intranet and DMZ subnet.
Groups for the homeworks 4-5 exercises:
- Hakan Evecek; Rodolfo Ortizmagdaleno; Guozhi Fu
- William Louis Bahn; Frank Xavier Gearhart; Beaux Sharifi
- Nick Sterling; Sarah Summers; Sarah Wahl
- Brian Ardrey; Balaji Ravi Badam; Duong Hang
- Paul Box; John Lefever; Bea Wilds
- Jeramie Reese; Candice Sonchar; Patrick Brannan
- Lindsey McGrath; Christine Weiss; Osama Khaleel
- Sujeeth Narayan; Ankur Patwa; Francisco Torres.
- Jason Cook; Michael Rudolph; Adrian Johnson
- Justin Gray; Michael Gerschefske; Joseph Lacont
- Ricardo Torres; Patrick Walpole; Matt Weaver; Ben White
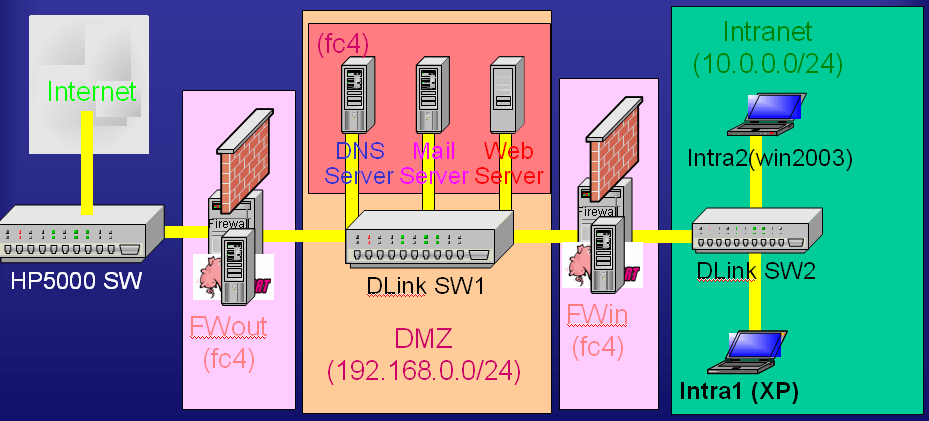
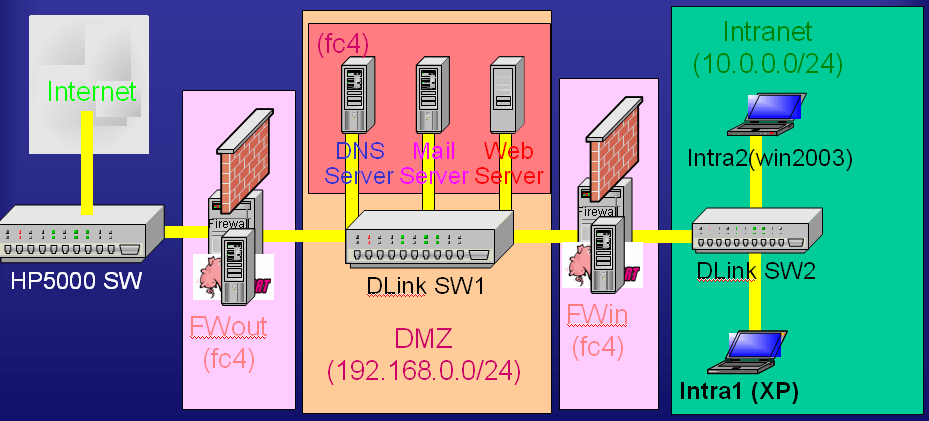
Configuration of Network Testbed:
- We have prepared three testbeds in EAS 143 for homeworks #4 and 5 exercises.
- Each testbed contains a stack of five PCs. The top three are installed with
Fedora Core 4. The bottom two are installedwith Windows 2003 server and Window
XP. Let us name the machines from top to bottom as machines 1, 2, 3, 4, and
5, and host names as fwout, dmzserver, fwin, intra1, and intra2. Note that
since we only have a 4 port KVM switch at this time. Do not worry about the
win2003 server. We will not use it.
- The top two Linux PCs contain two Ethernet interface cards and will be configured
as firewalls, outer firewall and inner firewall respectively.
- Two DLink switches and ethernet cables are provided for each testbed and
used to connect machines in DMZ and Intranet, and form the corresponding subnets.
- A 4-port KVM (Keyboard, Video, Mouse) switch is provided to connect four
of the five PCs to a set of Keyboard, Monitor, and Mouse. The KVM switch allows
you to switch between the consoles of those four PCs. The last PC is connected
manually. The switch is right on top of the PC stack. There is a selection
button to the right of the front panel. The red LED lights to its right indicating
which machine is currently being selected. Pushing the button will cycle through
the four machines.
- The following is the network topology diagram of the testbed:
- Four External IP addresses are assigned for each testbed:
- Testbed1: 128.198.61.38-41 (lab6-lab9.csnet.uccs.edu)
- Testbed2: 128.198.61.42-45 (lab10-lab13.csnet.uccs.edu)
- Testbed3: 128.198.61.46-49 (lab14-lab17.csnet.uccs.edu)
- Among those four external IP addresses, the first two are reserved for the
two DNS server, the thired one for FWout, the fourth one for the web server.
Since we have only one machine for DMZ server, we will only configure the
FC4 as web server for hw4. It will have 128.198.61.40 as IP address for testbed1.
- Before you start configuring the machines, we would suggest reboot them
so that you get a cleaner start. The team before you may have left the machines
in a strange state.
- After reboot them, use "iptables -F" and "iptables -t nat
-F" commands to reset the iptables on fwout and fwin.
- Step1. Physical Layer Connection:
- Connect the ethernet cables from the PCs to the designed switches.
- Due the tedious effort of this step. Skip this step.
- Step2. Configure the IP addresses
- For Fedora Core 4 Linux machine, use ifconfig eth0 or ifconfig eth1
command to configure the IP addresses.
- FWout:
- ifconfig eth0 128.198.61.38
- ifconfig eth0:1 128.198.61.39
eth0:n is called alias for eth0
- ifconfig eth0:2 128.198.61.40
- ifconfig eth0:3 128.198.61.41
- ifconfig eth1 192.168.0.1
This will be the default gateway for DMZ LAN
- Optional: Edit /etc/sysconfig/network to specify the host name and network
address.
- Optional: Edit /etc/sysconfig/network-scritps/ifcfg-eth0 and ifcfg-eth1
to specify the IP address, netmask, onboot, bootprotocol.
- The above two optional operations is to make the network configuration
permanent even after reboot.
- For Window XP and Win2003 server, Use Start | Settings | Control Panel
| Network Connections | Local Area Network | Properties | Internet Protocol
(TCP/IP)
to set static IP address, Subnet mask, and default gateway for the Intra2
win2003 server and Intra1 window XP.
- Note that since we only have 4 port KVM switch this time. Do not worry
about the win2003 server. We will not use it.
- Once you configure the IP address, you want to verify you have connectivity
among machines within the subnet.
- For example, from fwout, "ping 128.198.61.1" (default gateway),
"ping 192.168.0.2" (dmzserver), and "ping 192.168.0.3"
(fwin); from xp, "ping 10.0.0.1" (fwin).
- Note that at this point, from xp, "ping 192.168.0.1" will
not get response, since we did not have a routing table entry for 10.0.0.0/24
set up on fwout. We will do that in step 3.
- Step3. Configure the routing tables
- Use "route add defaut gw <gatewayIPAddress>" and "route
add -net <subnetAddress> -gw <gatewayTotheSubnet>" to
configure routing table properly in the firewalls and DMZ server.
- For example, on fwout, we use "route add default gw 128.198.61.1"
and "route add -net 10.0.0.0/24 -gw 192.168.0.3".
- With the first route commands, fwout should be able to ping 128.198.61.1
and Internet, including ping 128.198.1.250.
- You now can bring in any scripts you have prepare from outside to fwout
and then to fwin.
- The 2nd "route add -net" command to send responses back to
intra1.
- Note that here in this testbed, the default gateway for fwout is csnet
gatway with IP address128.198.61.1
- The default gateway for any DMZ macines including dmzserver and fwin
is fwout and the related gateway IP adress to them to use in their "route
add default gw" command is 192.168.0.1.
- You need run "route add -net" command to allow intranet machine
to talk to dmzserver, says for uploading web page to DMZ web server.
- The default gatway for any intranet machines including intra1 (XP) and
itra2 (Win2003server) will be fwin. I will let you figure out what it
is right gateway IP address to be used by intra1.
- Use Start | Settings | Control Panel | Network Connections | Local Area
Network | Properties | Internet Protocol (TCP/IP) to set static IP address,
Subnet mask, and default gateway for the Intra2 win2003 server and Intra1
window XP.
- After setting up the above routing tables, you still cannot ping outside
machine from dmzserver, fwin, and intra1. The reason is the two firewall
machines are not allowed packets to be foraded between its two ports.
- To allow that, we run "echo 1 > /proc/sys/net/ipv4/ip_forward"
command on both fwout and fwin.
- Now try ping 192.168.0.1 (fwout) from intra1. You will get response
because the ICMP messages are forwarded by fwin. Same when you ping 10.0.0.51
from dmzserver.
- But you will find that you can not ping 128.198.1.250 (Internet; UCCS
DNS server) from any machine except fwout.
- Why this that? The reason is all the ICMP message from those machines
will have private LAN address in their source IP address and their responses
can not be routed back . To solve that, we need SNAT service on fwout.
See Step4.
- Step4. Configure firewalls on FWout and FWin with proper firewall rules
to provide DNAT/SNAT services.
- The simplest DNAT and SNAT rules for testbed 3 are
iptables -t nat -A PREROUTING -p TCP -i eth0 -d
128.198.61.47 --dport 80 -j DNAT --to-destination 192.168.0.2
iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
Here I assume 128.198.61.47 is web server external IP address. Internally
the web server is run on dmzserver machine with 192.168.0.2.
- Now you should be able to access web pages in Internet from any of the
machines in the testbed and ping 128.198.1.250.
- Also if you login to blanca, say using "ssh -l <yourlogin>
blanca.uccs.edu" and type "lynx 128.198.61.47" you should
be able to get a web page with heading "CSNET Testbed 3 for CS591".
If you did not get web page, try check if the apache web server is running
on dmzserver. Use "service httpd restart" to start it.
- Email me the browser result such as lynx 128.198.61.47 as a proof that
the DNAT is set up correctly.
- For more complete and secure firewall rules, use the DMZ
firewall shell script as a template. Replace with our network IP address
and network info.
http://iptables-tutorial.frozentux.net/scripts/rc.DMZ.firewall.txt
- Verify DNAT by login to blanca and issue the http request to dmzserver.
You can use lynx a text-based for such test. Capture the http response
from web server as a proof.
- Verify SNAT by accessing web site in Internet from intra1.
- Step5. Check on the /var/log/message or /var/log/secure on FWout. Examine
who are trying to break in using ssh with root.
- Note that we have set "PermitRootLogin no" in /etc/ssh/sshd_config
therefore the firewall by default will not accept root user access from
Internet.
- Add firewall rules to drop packets from those intruders.
- If there is no such attack, find out the IP addresses of Blanca or a
EAS 149 Lab pc; add firewall rule to block its access to the DMZ web server;
verify indeed the access is blocked on that specific machine; make sure
others still able to access.
- Observe if any more log occurs after the above firewall rules are inserted
- Step6. Add to firewall rules to disallow intra2 to connect to Internet.
- Save the firewall rules and network configurations (ifconfig, netstat
-rn) as a file for submission.
Questions:
- Q1. In Step 5, we indicate that the remote ssh root access is turned off.
What is the benefit of adding firewall rules to drop packets from those intruders?
What rules you added? What chains you have added those rules?
- Q2. Similar to the DMZ firewall example in iptables tutorial (http://iptables-tutorial.frozentux.net/scripts/rc.DMZ.firewall.txt)
The Sonic Firewall has three ports: one connects to Internet; one connects
to DMZ subnet; and the last connects to the intranet. Their network topology
is different from that of the above testbed, which has two firewall machines
connecting through the DMZ LAN. Discuss what are the trade-off of these two
different configurations based on the eight deisgn principle.
- Q3. Critic on the resource/machine assignments for this exercise: Suggest
any improvement on the resource assignment