compiling keystone
keystone1.0 uses 2 security packages
cryptolib-1.2 -- for encryption/decryption key
openssl-0.9.x -- for certificate handling.
getting hold of cryptolib-1.2 by Jack Lacy is a tough task and why keystone uses both cryptolib and openssl is unknown. work on cryptolib has stopped a few years back. u can download it from http://opensores.thebunker.net/pub/mirrors/cryptolib/
problems
1) with out rsa licence u cannot get RSA code to work.
fixes) replace the rsa.c with the rsa code fix for non licence available for 1.1
2) on linux boxes pseudo random genarator doesn't work properly as multiple setjmp calls to the same location creates problems.
fixes) download the file from..........
latest versions of openssl can be downloaded from http://www.openssl.org/
Keystone 1.0 comes with the following programs and a library for different components and functions
"keyserver0" is a key server program with embedded registrar.
"keyserver" is a key server program without embedded registrar.
"registrar" is a registrar program.
"specwriter" is a specification writer program.
"libks.a" is a library for client control functions.
i have tested keystone with embedded registrar.
problems certificate files are outdated.
fix had to generate a new set of certificates
certificate generation script can be downloaded at ...........
running keystone
# ./keyserver0
Specification? spec.2
*** Request port is 20002.
*** Registrar setup port is 30002.
access control none
WARN: no access control info
WARN: no access control file
Running the client program
# ./sslclient
Registrar address and client registration port
(or "keyserver" for a keyserver with embedded registrar)? keyserver
Keystone context file (or "interactive")? ctx.2
Key server address? 128.198.60.195
registration with keyserver ave registration time 54687 50781 3906 us
Operation? Operation? join g1
Operation? print g1
Key g1 100000(2): a0b48be1 f519a47e 91d9f310 07d721aa a0b48be1 f519a47e
Note. acl file format specified in keystone's userguide is not right. u need to speficy all details
"/C=US/ST=Colorado/L=Colorado Springs/O=University of ColoradoatColorado< /FONT> Springs/OU=SGFR/CN=client/Email=client@cs.uccs.edu" g1 end
Installing jabber.
jabber can be downloaded from http://jabberd.jabberstudio.org/downloads/
if u get an error message on running the error message
# ./jabberd/jabberd -h oblib.uccs.edu
./jabberd/jabberd: error while loading shared libraries: libpth.so.14: cannot open shared object file: No such file or directory
type the following commands at the prompt and try again
# LD_LIBRARY_PATH=/usr/local/lib
# export LD_LIBRARY_PATH
to enable conference download the conference module from http://jabberd.jabberstudio.org/downloads/
points of interception for integrating keystone for secure group communication frame work
............
..............
Status of SGFR
1.1 project Goal
.
.
.
.
.
.
1.2 project status
right now we have succesfully installed keystone for group key management and jabber server for instant message.
jabber
In essence, a Jabber server does the following:
accepts TCP socket connections from compatible clients and server-side components
manages XML streams to and from those clients and components
delivers the core Jabber data types (<message/>, <presence/>, and <iq/>) to authorized clients and components
maintains session information for connected clients (usually IM users)
if necessary, opens connections to and validates connections from other Jabber servers, then routes data to them
stores information on behalf of components and especially IM users, including each user's contact list and some client preferences
so jabber follows a client server model
Keystone
keystone has the following components
"keyserver0" is a key server program with embedded registrar.
"keyserver" is a key server program without embedded registrar.
"registrar" is a registrar program.
"specwriter" is a specification writer program.
"libks.a" is a library for client control functions.
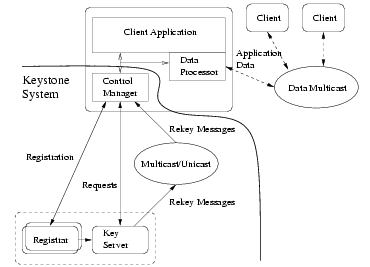
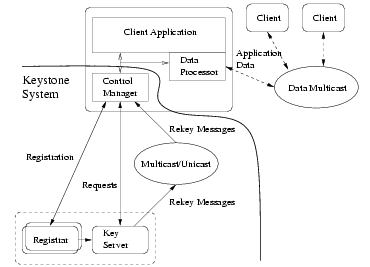
there are many client control managers (one for each client), one or more registrars, and only one key server. the control manager of a client is responsible for client control functions e.g., sending requests and processing rekey messages. Each client also has a data processor which is not part of keystone. A data processor uses group keys from its control manager to perform application data functions, e.g., encryption, decryption, signing and verificaton. A registrar authenticates the identities of clients and distributes an authenticated client's individual key between the client and key server. the key server processes requests from clients, changes keys, and distributes new keys to clients using rekey messages. Keystone can deliver rekey messages to clients using unicast or mulicast.
currently we are working on developing a data processor that can be used with jabber for interaction with the instant messenger